NetConf Over Transport Layer Security
Transport Layer Security (TLS) is a cryptographic protocol that uses mutual certificate-based authentication and provides a secure and reliable connection between two devices. It is a successor to the Secure Sockets Layer (SSL) protocol. When a Netconf session is established over TLS, the NetConf server acts as the TLS server, and the NetConf client must act as the TLS client.
NetConf sessions over TLS provide some advantages over sessions that use SSH. Whereas SSH authenticates a client by using credentials (username and password) or keys, TLS uses certificates to mutually authenticate both the client and the server. Certificates can provide additional information about a client, and they can be used to securely authenticate one device to another. Thus, while NetConf sessions over SSH work well for manually managing individual devices, NetConf sessions that use TLS enable secure device-to-device communication for more effectively managing and automating devices in large-scale networks.
TLS subsystem logs are integrated with the system logger (syslog) and appear (along with other OcNOS logs) in /var/log/message with the tag TLS_SUBSYS.
TCP port number 6513 is used by the NetConf server to listen for TCP connections established by NetConf over TLS clients.
Topology
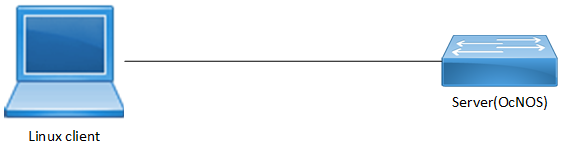
Netconf over TLS Topology
Client Configuration
1. Generate CA authority key and certificate on TLS client:
openssl req -newkey rsa:2048 -new -nodes -x509 -days 3650 -keyout rootCAKey.pem -out rootCACert.pem
2. Generate client key and certificate on client:
a. Create a new file named ClientCertReq.config with this content:
[req]
distinguished_name = dn
prompt = no
[dn]
CN = 10.12.65.10 ---------- > <Apply TLS client IP here>
C = IN
L = BNG
O = IPI
OU = IPI-QA
openssl req -newkey rsa:2048 -keyout ClientKey.pem -out ClientCert.csr -config ./ClientCertReq.config -nodes -days 100
3. Client certificate signing:
openssl x509 -req -sha256 -in ClientCert.csr -CA rootCACert.pem -CAkey rootCAKey.pem -CAcreateserial -out ClientCert.pem -days 365
4. Server certificate signing:
openssl x509 -req -sha256 -in ServerCert.csr -CA rootCACert.pem -CAkey rootCAKey.pem -CAcreateserial -out ServerCert.pem -days 365
5. Manually import (SCP) signed server certificate and CA-root certificate to OcNOS (/usr/local/etc/tls/certs).
• File should be in PEM format for CA-root certificate and named cert.pem (/usr/local/etc/tls/certs/ca.pem).
• OcNOS server certificate file should be in PEM format and named cert.pem (/usr/local/etc/tls/certs/cert.pem).
6. Establish TLS session using the below command on the client side:
connect --tls --host 10.12.89.152 --port 6513 --cert /root/QUX/ClientCert.pem
--key /root/QUX/ClientKey.pem --trusted /root/QUX/rootCACert.pem
Note: This example uses the Netopeer2 command as NetConf client over TLS.
Server Configuration
Generate server private key and CSR request on the TLS server:
>enable | Turn on privileged mode. |
#crypto pki generate rsa common-name ipv4 10.12.93.111 | IP address used by TLS clients to connect to the NetConf server running on OcNOS. |
#show crypto csr | Show Certificate Signing Request |
Validation
On TLS server:
# show crypto csr
-----BEGIN CERTIFICATE REQUEST-----
MIICXDCCAUQCAQAwFzEVMBMGA1UEAwwMMTAuMTIuOTMuMTExMIIBIjANBgkqhkiG
9w0BAQEFAAOCAQ8AMIIBCgKCAQEA7dTLZpS7sTCrFdP4gQD6X4+PHtYKK7jQdSaM
WaX20dkPqxN8/6VHuY3+fE13eeUSPrDbdSOzPq6f/Rdd/xG76Qi95yYKZnUkTz1/
sF50LfdxL2u+Xg25TA4+Lh6EHYxbmLwX6/o4b8E+78CH+NftH6g1/2YN14PC3lI1
Jlar+YEAzlyy8q1RAHbiazyJmgR0n4KxdtU/c/nzU8zP4OWtJdNquAAMkQUcWwBg
0a88FpFEm5SkQRslLX2BdofpO0SCiMJVkYRJH8yirxKwHx7JBg7EtDovofY585rj
zBZBTycsWYrpWGh+YUm+5ZbEHN+NC2r9UqvLVuHyYWRPB40jxQIDAQABoAAwDQYJ
KoZIhvcNAQELBQADggEBAD0/4MxtfJrz3jeBAMUwIjTBFauTI2rJ0AMxjIcPfvel
wLi/nK4HBU3Ucg9yUqfPYwfi3gLa901AJT5UVPZV0C783nNBrR9GRa91rL0+0Ksa
hptlTCvFug/N7oEIADQ2IHskNTyCSW7MeJaz06amhiGHp+QNjNulAmsXUjPOzKsJ
OILOmBvD10N+GvtvBMhJrxDKzCda9auSdk1If1BRdfmNttnfthoK3PWK5kmkyhlr
l4mz3Mvd9E5UvsMfL8u72FibwaHa3b862/YQdbidN2LS8xjCZTxeitbJooLzywhb
hR99BENUG8zTbmIa8BD2Nt8F3mlo/31kD8eO2QTLqfI=
-----END CERTIFICATE REQUEST-----
PE3#
Note: You should copy and paste the output of the above show command into the ServerCert.csr file on the client.