DHCP Snooping
Overview
DHCP snooping is a series of techniques applied to ensure the security of an existing DHCP infrastructure. It is a security feature that acts like a fire wall between untrusted hosts and trusted DHCP servers. It is a layer-2 security technology built into the operating system of a capable network switch that drops DHCP traffic determined to be unacceptable.
The fundamental use case of DHCP snooping is to prevent unauthorized (rogue) DHCP servers offering IP addresses to DHCP clients. Rogue DHCP servers are often used in 'man-in the middle' or 'Denial of Service' attacks from malicious purpose. Similarly DHCP clients (rogue) can also cause 'Denial of Service' attacks by continuously requesting for IP addresses causing address depletion in the DHCP server.
The DHCP snooping feature performs the following activities:
• Validates DHCP messages received from un-trusted sources and filters out invalid messages.
• Rate-limits DHCP traffic from trusted and un-trusted sources.
• Builds and maintains the DHCP snooping binding database, which contains information about un-trusted hosts with leased IP addresses.
• Utilizes the DHCP snooping binding database to validate subsequent requests from un-trusted hosts.
DHCP snooping is enabled on a per-VLAN basis. By default, the feature is inactive on all VLANs. You can enable the feature on a single VLAN or a range of VLANs.
Topology
.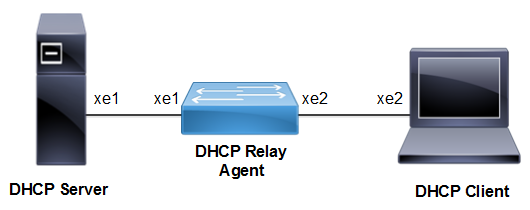
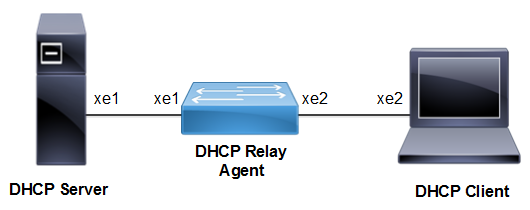
DHCP Snooping topology
Configuration Guidelines
When configuring DHCP snooping, follow these guidelines:
• DHCP snooping is not active until you enable the feature on at least one VLAN, and enable DHCP snooping globally on the switch.
• Before globally enabling DHCP snooping on the switch, make sure that the device acting as the DHCP server is configured and enabled.
• If a Layer 2 LAN port is connected to a DHCP server, configure the port as trusted by entering the ip dhcp snooping trust interface configuration command.
• If a Layer 2 LAN port is connected to a DHCP client, configure the port as un-trusted by entering the no ip dhcp snooping trust interface configuration command.
Procedures
The following subsections provide examples of how to enable and configure DHCP Snooping.
Enable the Ingress DHCP-snoop TCAM group
#configure terminal | Enter Configure mode. |
(config)#hardware-profile filter dhcp-snoop enable | Enable the ingress DHCP-snoop TCAM group |
(config)#commit | Commit Candidate config to running-config |
Disable the Ingress DHCP-snoop TCAM group
#configure terminal | Enter Configure mode. |
(config)# hardware-profile filter dhcp-snoop disable | Disable the ingress DHCP-snoop TCAM group |
(config)#commit | Commit Candidate config to running-config |
Enable the Ingress DHCP-snoop-IPv6 TCAM group
#configure terminal | Enter Configure mode. |
(config)#hardware-profile filter dhcp-snoop-ipv6 enable | Enable the ingress DHCP-snoop-IPv6 TCAM group |
(config)#commit | Commit Candidate config to running-config |
Disable the Ingress DHCP-snoop-IPv6 TCAM group
#configure terminal | Enter Configure mode. |
(config)# hardware-profile filter dhcp-snoop-ipv6 disable | Disable the ingress DHCP-snoop-IPv6 TCAM group |
(config)#commit | Commit Candidate config to running-config |
Enable DHCP Snooping Globally
#configure terminal | Enter Configure mode. |
(config)#bridge 1 protocol mstp | Create MSTP or IEEE VLAN-bridge. |
(config)#ip dhcp snooping bridge 1 | Enable DHCP Snooping on the bridge |
(config)#commit | Commit Candidate config to running-config |
Enable DHCP Snooping on a VLAN
#configure terminal | Enter Configure mode. |
(config)#vlan 2 bridge 1 | Configure a VLAN for the bridge. |
(config)#ip dhcp snooping vlan 2 bridge 1 | Enable DHCP Snooping on the VLAN 2 |
(config)#commit | Commit Candidate config to running-config |
Validation
OcNOS#show hardware-profile filters
Note: Shared count is the calculated number from available resources.
Dedicated count provides allocated resource to the group.
If group shares the dedicated resource with other groups, then dedicated
count of group will reduce with every resource usage by other groups.
+--------------------+---------+---------------+----------------------------+
| | Free | Used | Total Entries |
| Unit - TCAMS | Entries |---------------|----------------------------|
| | | % | Entries | Total | Dedicated | shared |
+--------------------+---------+-----+---------+-------+-----------+--------+
0 DHCP-SNOOP 9717 0 5 9722 1018 8704
0 DHCP-SNOOP-IPV6 9717 0 6 9723 1019 8704
Configuring the Ports Connected to DHCP Server and DHCP Client
#configure terminal | Enter Configure mode. |
(config)#interface xe1 | Specify the interface xe1 to be configured, and Enter interface mode |
(config-if)#switchport | Configure the interface as a switch port. |
(config-if)#bridge-group 1 | Associate the interface xe1 with bridge-group 1. |
(config-if)#switchport mode access | Configure the port as an access port |
(config-if)#switchport access vlan 2 | Bind the interface VLAN 2 to the port |
(config-if)#exit | Exit interface mode. |
(config)#interface xe2 | Specify interface xe2 to be configured connected to server. |
(config-if)#switchport | Configure the interface as a switch port |
(config-if)#bridge-group 1 | Associate interface xe2 with bridge-group 1. |
(config-if)#switchport mode access | Configure the port as an access port. |
(config-if)#switchport access vlan 2 | Bind the interface VLAN 2 to the port |
(config-if)#exit | Exit the config mode. |
(config)#commit | Commit Candidate config to running-config |
(config)#exit | Exit the config mode. |
Configuring Trusted and Un-trusted Ports
Usually the port connected to server is configured as trusted port and the ports connected to client is configured as un-trusted port.
In this example, xe2 is connected to the DHCP client and xe1 is connected to the DHCP server.
• Configure xe2 connected to DHCP client as un-trusted port.
• Configure xe1 connected to the DHCP server as trusted port.
#configure terminal | Enter Configure mode. |
(config)#interface xe1 | Specify the interface to be configured |
(config-if)#ip dhcp snooping trust | Enable the port as trusted. |
(config)#commit | Commit Candidate config to running-config |
(config)#interface xe2 | Specify the interface to be configured |
(config-if)#no ip dhcp snooping trust | Disable the port as trusted. |
(config-if)#exit | Exit interface mode |
(config)#commit | Commit Candidate config to running-config |
DHCP Snooping Operation
1. Configure DHCP server that is connected to DHCP Snooper through trusted port.
2. Request an IP address from the DHCP client connected through the un-trusted port.
3. DHCP client broadcast the DHCP DISCOVER message to the switch.
4. DHCP server responds to the DHCP DISCOVER message with DHCP offer message to the client.
5. Once the DHCP OFFER is received by the client, it sends an DHCP REQUEST to the server.
6. DHCP server validates the request from the client and sends DHCP ACK with the offered IP address to the client with the lease time.
7. DHCP Snooper creates an entry for the above operation into the binding table which includes the MAC address of the host, the leased IP address, the lease time, the binding type, and the VLAN number and interface information associated with the host.
8. DHCP Snooper clears the entry in the binding table once the client sends the DHCP RELEASE query.
Validation
The show running-config ip dhcp snooping command displays the DHCP snooping commands configured on the device in question
#show running-config ip dhcp snooping
!
!
ip dhcp snooping bridge 1
ip dhcp snooping vlan 2 bridge 1
interface xe1
ip dhcp snooping trust
!
The show ip dhcp snooping bridge 1 command displays the configured information about DHCP Snooping.
#show ip dhcp snooping bridge 1
Bridge Group : 1
DHCP snooping is : Enabled
DHCP snooping option82 is : Disabled
Verification of hwaddr field is : Disabled
Rate limit(pps) : 100
DHCP snooping is configured on following VLANs : 2
DHCP snooping is operational on following VLANs : 2
DHCP snooping IP Source Guard is configured on the following Interface
Interface Trusted
--------------- -------
xe2 Yes
The show ip dhcp snooping binding bridge 1 command displays the binding table entries associated with un-trusted interfaces.
#show ip dhcp snooping bridge 1
Bridge Group : 1
DHCP snooping is : Enabled
DHCP snooping option82 is : Disabled
Verification of hwaddr field is : Disabled
Rate limit(pps) : 100
DHCP snooping is configured on following VLANs : 2
DHCP snooping is operational on following VLANs : 2
DHCP snooping trust is configured on the following Interfaces
Interface Trusted
-------- -------
Xe1 Yes
DHCP snooping IP Source Guard is configured on the following Interfaces
Interface Source Guard
------- -----------